SCADA Security: Phishing Season is Open
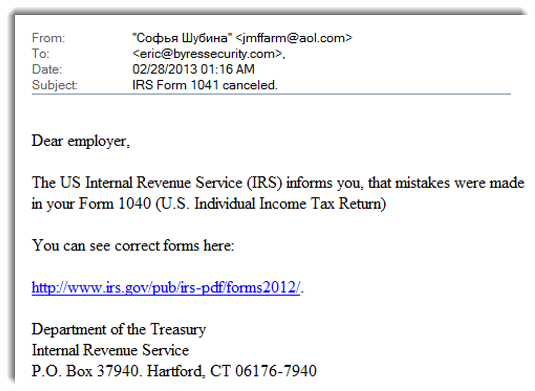
Last week I received am email (shown further down on this page) purporting to be from the US Internal Revenue Service (IRS).
Phishing, like fishing, can be profitable. Image Credit: Fotopedia
Notice that the US Internal Revenue Service now uses Cyrillic script on its staff email addresses! And they use AOL as an email service, rather than irs.gov. (Is the US budget sequestration really hurting that badly?  )
)
The third fun item is that the link you are supposed to click on (irs.gov/pub/irs-pdf/forms2012/) actually resolves to prospectrealty.net/wp-content/plugins/Bridge-Book-Printer/forms.htm.
(Note to Prospect Realty – you might want to secure your web site a little better.)
Beware Industrial Security Pros: Phishing Season is Open
Obviously, this email is a phishing attack. The creators of the email want me to click on the fake IRS link. If I did, my browser would be directed to the Prospect Realty website they have hacked. There I would either see a page that looked like an IRS log-in page (so the crooks could steal any confidential corporate information I enter) or the site would try to download some nasty Java applet that would take over my computer (assuming I hadn’t patched Java recently).
This phishing attack is so crude and so obvious that it is funny.
But in another way, it isn’t funny at all.
Phishing is Profitable for Attackers
Attacks like this only continue if they make their creators money. And the criminals behind them have very simple and effective ways to determine if their attacks are effective. They launch the email and then count the number of suckers that click in the next few hours. If they don’t get any clicks, they try something different. If they get enough victims, they launch the attack again against a new list of email addresses.
Now I received this same phishing email multiple times over several days - which leads me to believe that it was effective for the bad guys. Poor sods were clicking on the links. And these aren’t just any poor sods. Remember that this email is addressed to employers – not grandma or grandpa. So the email is an attack on the accounting teams in corporations, a group one might hope is very computer savvy.
Not All Cyber Security Threats are Stuxnet Quality
So what is my point? In the SCADA and ICS world we worry a lot about highly sophisticated threats like Stuxnet attacking our companies. Yet it seems that completely amateurish attacks work too (remember Shamoon?). Crooks don’t need sophisticated teams of hackers to be successful in cybercrime. All they need are employees to be so poorly trained that they click on even the most obvious phishing email.
Industry has a long way to go to make both IT and SCADA systems truly secure. To get there, it will cost a lot of money. But it seems like there are a lot of baby steps that still aren’t being taken on the road to security. Maybe it is time to take another look at those.
Does your organization train employees to be wary of phishing attacks? Do you have any “phishing” stories to share?
Related Content to Download
|
White Paper: "Using ANSI/ISA-99 Standards to Improve Control System Security" |
Note: ANSI/ISA-99 Standards have recently been renamed ISA/IEC 62443 Standards.
Related Links
- IRS, Webpage: Report Phishing
- Blog: Defense in Depth is Key to SCADA Security – Part 1
- Blog: Defense in Depth: Layering Multiple Defenses - Part 2 of 2
- Blog: Summing up Stuxnet in 4 Easy Sections - (plus Handy Presentation)
- Blog: Simpler SCADA Security Beats More User Training
- Blog: Shamoon Malware and SCADA Security – What are the Impacts?



Add new comment